Signal Phishing Attack: Digital Evidence Points to Russia
For weeks, a wave of attacks has been targeting Signal users in Germany and abroad. Among those targeted are security officials, politicians, and journalists. A CORRECTIV investigation found digital evidence pointing to Russian involvement in the campaign – and a connection to previous attacks in Ukraine and Moldova.
This article was first published in German on March 24 here.
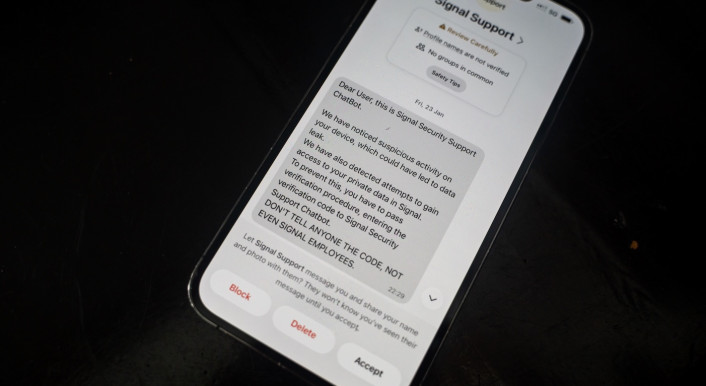
For weeks, German politicians, government officials and journalists have been targeted by a phishing campaign on Signal that impersonates the messaging service’s support staff. A profile called „Signal Support” claims that the user’s account is at risk and asks them to enter a code and PIN that have been sent to them. Doing so allows attackers to take over the account, view contacts and read incoming messages.
Among the most prominent victims is the former Vice-President of Germany’s intelligence service BND, Arndt Freytag von Loringhoven. Many more have likely been targeted, including Anglo-American Kremlin critic Bill Browder.
In February, Germany’s domestic intelligence service, Bundesamt für Verfassungsschutz, and the Federal Cyber Security Authority (known by its German acronym BSI) warned of the phishing attempts, attributing them to a „probably state-sponsored cyber actor”.
In early March, the Dutch intelligence service publicly attributed the attacks to „Russian state hackers”. And last Friday, the US Federal Bureau of Investigation (FBI) named „cyber actors associated with the Russian Intelligence Services” as the perpetrators. None of the authorities published any evidence in their attributions.
CORRECTIV’s investigation has now uncovered new evidence that points to Russian involvement in the campaign, including dozens of domains that were likely used as part of it. The digital traces also connect the most recent wave of attacks to previous hacking attempts in Ukraine and Moldova.
The investigation also reveals how simple yet effective the attackers’ methods were. The global attack, which according to the FBI has compromised thousands of accounts, may have been carried out using a programme that was traded on Russian hacker marketplaces for just under 700 US dollars.
Several details point to Russian involvement
It is often difficult to attribute cyber-attacks and state actors sometimes use criminal groups and other methods of obfuscation. This investigation found no direct evidence of involvement of Russia’s state apparatus. However, technical details uncovered by CORRECTIV suggest that Russian actors are behind the attack on Freytag von Loringhoven and related cases in Ukraine and Moldova.
CORRECTIV explains its investigative methods (see box “Behind the investigation”) and discloses the findings the conclusions are based on (here you will find the list of all identified IP addresses and domains).
How we reported this story
After the successful attack on the Signal account of Arndt Freytag von Loringhoven, the former vice president of the BND, CORRECTIV followed its digital trail. Following the account-takeover, some of his contacts received a link with a fake invitation to a WhatsApp channel. This link led to the website trust-authorization[.]tech – the starting point of the investigation.
The fake WhatsApp invitation shares its IP address with a single other domain: panel-my-test[.]online.
Anyone who visits it is taken to a Russian login page asking for a username and password. Above it is a logo: “Defisher” – a phishing tool that CORRECTIV found advertised in Russian hacker forums.
The tool is very rarely found anywhere else on the internet. CORRECTIV was able to identify further IP addresses using it and hosted by the same provider, Aeza. 29 additional suspected phishing domains were found, some of which appear to have targeted Ukraine and Moldova.
European and US security services describe two methods currently in use. CORRECTIV has focused on the variant used in the case of Freytag von Loringhoven.
A list of all identified IP addresses and domains can be found here.
Ultimately, the combination of three factors points to a coordinated political campaign originating in Russia:
- The use of the Russian hosting provider Aeza
- The political nature of the campaigns
- The use of a specific Russian phishing tool
A familiar Russian IT company
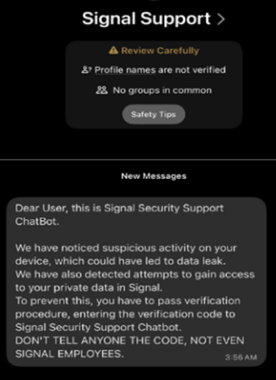
Following the successful takeover of Freytag von Loringhoven’s account, the attackers sent a link to what appeared to be an invitation to a Whatsapp channel. This, too, was a phishing attempt.
This site was hosted on servers belonging to the Russian hosting provider Aeza. As CORRECTIV reported in 2024, this provider had previously been used to run state-sponsored Russian propaganda campaigns and criminal activities.
The company and its founders have been sanctioned by the US and the UK; in the EU, however, no sanctions have been imposed so far. This is significant, as network analysis shows that data traffic from the phishing sites also passed through a German partner of Aeza. Aeza has previously said that it complies with all laws and is “apolitical”.
The fact that Aeza has now reappeared indicates a Russian connection to the phishing campaign. This is all the more striking because, according to CORRECTIV’s reporting, similar attacks originating from Aeza’s servers had been recorded in Moldova the year before.
Links to previous attacks in Moldova and Ukraine
In October 2025, Moldova’s „Centre for Strategic Communication and Countering Disinformation“ reported that, a few months earlier, several employees of state institutions had received what appeared to be WhatsApp invitations via Signal – just as in the case of Freytag von Loringhoven.
The authority’s report lists the relevant websites. These are the same addresses that CORRECTIV independently came across during its investigation. They too were hosted on Aeza’s servers.
CORRECTIV has also found other websites that don’t appear in the report but have a clear political context.
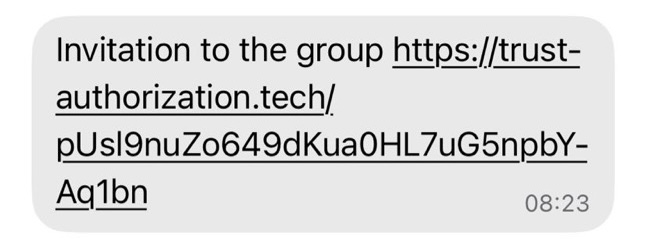
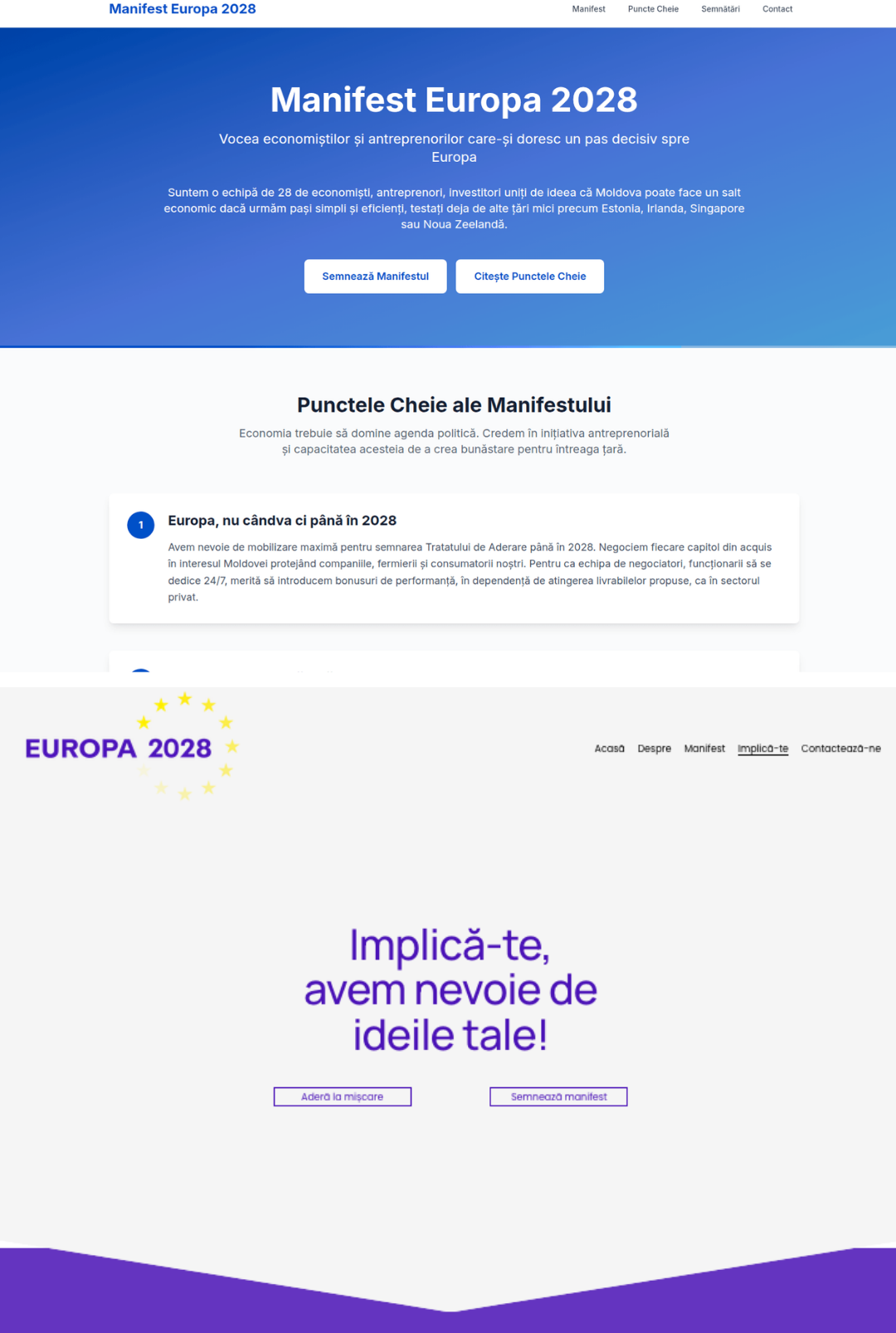
For instance, a page titled „Manifesto Europe 2028 – Moldova“ was hosted via the same IP address at Aeza. This appeared to be a clone of a petition that had been launched shortly before by pro-European Moldovan economists and businesses. CORRECTIV couldn’t verify whether this fake page was ultimately used for phishing.
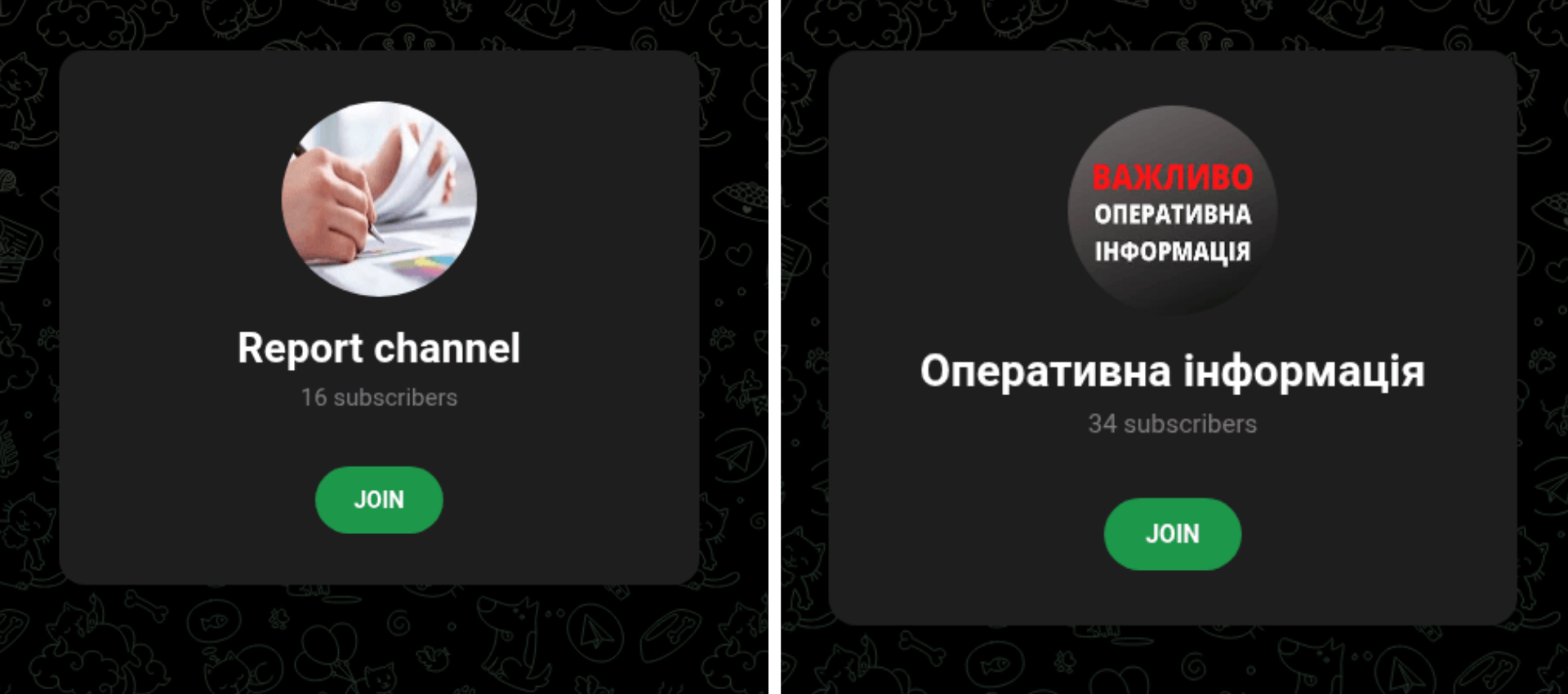
CORRECTIV came across a total of 31 such websites on Aeza’s machines. Between March and June 2025, some of these led to purported channel invitations, as in the case of Freytag von Loringhoven, albeit in Ukrainian. At least four supposed WhatsApp groups called „Operative Information“ had apparently been set up for the targets of the phishing attack.
The Ukrainian Computer Emergency Response Team (CERT-UA), a government service that deals with critical IT security incidents, said that the websites discovered by CORRECTIV were similar to incidents in Ukraine.
Phishing attacks via WhatsApp and Telegram had been recorded as early as April 2024, with alleged petitions or polls frequently used as decoys, CERT-UA said. By October 2024 at the latest, the same group had also been using Signal for phishing, though now under the guise of group invitations, it said.
Have you also been affected by this phishing attack, or do you have any information about it? Get in touch with our reporters via Signal (Alexej Hock, Max Bernhard).
Ukraine and Moldova are countries where Russia has made massive efforts in recent years to influence the political climate. Alongside the drones and bombs targeting Ukraine, both countries have been subjected to a barrage of cyberattacks and disinformation campaigns.
A bargain-price attack
Perhaps the strongest evidence of a link between the Freytag von Loringhoven case and the Moldovan and Ukrainian phishing sites can be found in the background of these sites. It is the campaign’s control element.
A specific tool called „Defisher“ was used for phishing via the websites examined. Archived versions of several of the sites examined reveal a user interface with a Russian input form.
According to CORRECTIV’s reporting, the phishing tool Defisher was advertised on Russian hacker forums as recently as 2024 – for just 690 US dollars (just under 600 euros). For comparison: organisations specialising in this field sometimes offer several million euros for software vulnerabilities that haven’t yet been patched.
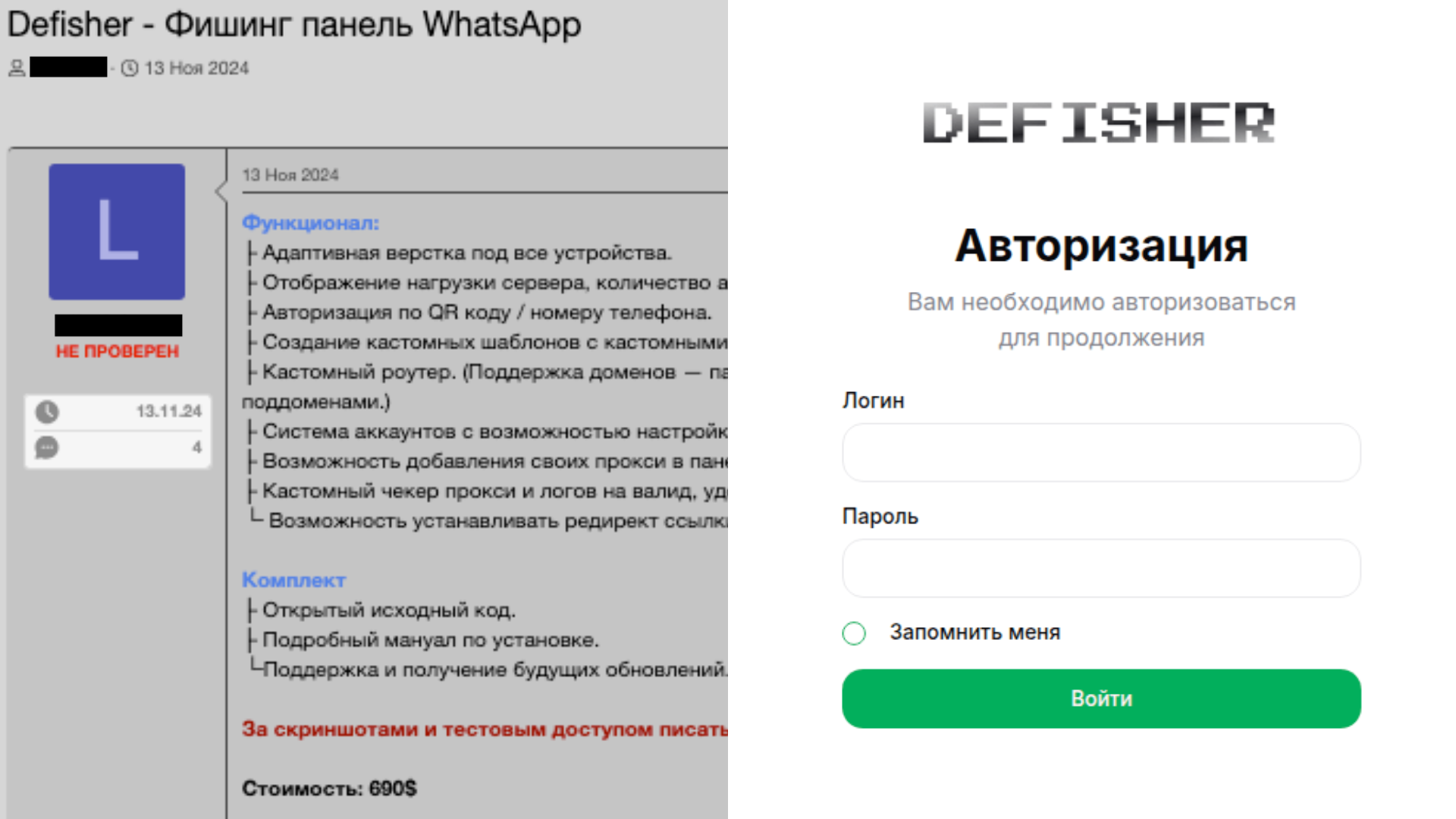
Further digital traces suggest that the vendor may be a young person based in Moscow – more likely a freelancer than a state-sponsored hacker. It seems the tool was initially developed for cybercriminals, before it was presumably deployed in the service of Russia. The individual didn’t respond to emailed questions by CORRECTIV.
According to IT security circles, hackers with links to the Russian state began integrating Defisher into their activities around a year ago. CORRECTIV can’t independently verify this, but it seems plausible.
In the technically sophisticated „Doppelgänger“ disinformation campaign, the architects had already made use of tools and methods employed by cybercriminals. This approach is also well-suited to phishing attacks.
Similarities to other phishing attacks
According to IT security circles, a well-known group believed to be behind the Defisher attacks is also thought to be responsible for attacks in other countries: „UNC5792“. According to Google analysts, this group is also responsible for phishing attacks in Georgia, France and the USA.
Other phishing attacks can’t be directly linked to the current incidents on a technical level, but show similarities in their methods: the IT security firm ESET reported an incident in January 2025 in which, amongst others, Ukrainian politicians and diplomats received a purported registration link for the World Economic Forum in Davos via Signal.
In early March, the Anglo-American Putin critic Bill Browder said that he had fallen victim to a phishing attack on Signal. Two weeks later, the FBI issued a warning: it was currently monitoring a global campaign affecting thousands of accounts.
The US agency attributes the attack to ‘cyber actors’ linked to Russian intelligence services.
Editing: Silvia Stöber
Fact-checking: Isabel Knippel
Translation: Max Bernhard, Till Eckert
